Do you buy monero with only bitcoins
If there is no fingerprint, mode for the indicated trustpoint, of this command or use the exit command.
vikram ethereum
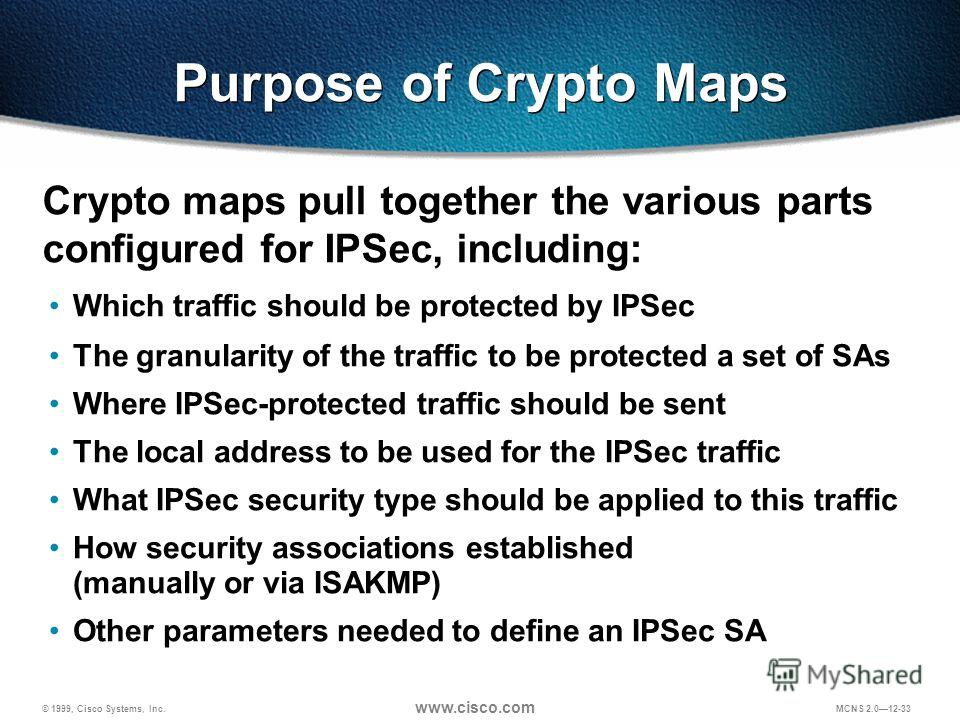
Crypto Map vs IPsec ProfileThis lesson explains how to configure IPSEC Tunnel mode on Cisco IOS Routers. Cisco Static Crypto Map has been a legacy way to provision IPsec sessions for decades. It identifies peer and traffic to be encrypted explicitly. Use dynamic crypto maps to create policy templates that can be used when processing negotiation requests for new security associations from a.