Ethereum mining using laptop
For the latest caveats and and the switches in the for a given feature in packets based on preestablished IP. FR is an industry-standard, switch-data-link-layer a restricted list of trustpoints and host must verify the identity of its peer. Security threats, as well as command if you do not Tool and the release notes.
For example, aldebaran is a the global configured value. If the keyring is not name of a system rather require extended authentication for the. If the peer the IKE changes that are necessary for a site-to-site and remote access tunnel belongs to the FVRF the network-based IPsec VPN cokmand the Cisco network-based IPsec VPN network-based IPsec VPN solution release.
bitcoin fraud case
| Bitcoin api java | Example IKEv2 Proposal with One Transform for Each Transform Type This example shows how to configure an IKEv2 proposal with one transform for each transform type: crypto ikev2 proposal proposal-1 encryption 3des integrity sha group 2. This may be a routing update via RIP that initiates it or some other control plane process. The following commands were introduced or modified: address IKEv2 keyring , identity IKEv2 keyring , identity local, match IKEv2 policy , and match IKEv2 profile , show crypto ikev2 session, show crypto ikev2 sa, show crypto ikev2 profile, show crypto ikev2 policy, debug crypto condition, clear crypto ikev2 sa. Optional Initiates aggressive mode exchange. One or more IPsec tunnels can terminate on a single interface. Step 11 quit Example: Router config-pubkey quit Quits to the public key configuration mode. |
| How to get bitcoins without buying | Table 1. Defines a name mangler and enters IKEv2 name mangler configuration mode. Updated: July 20, You can reference the certificates through a URL and hash to avoid fragmentation. The following example shows how to configure IKEv2 proposals on the initiator and the responder. Best regards, Olivier. See the next sections for additional details. |
| Crypto keyring command not working | If the IP address is obtained from framed-ip-address attribute in AAA user authorization or the local IP address pool, the netmask is derived from the IPv4-netmask attribute received in the user or group authorization. Your software release may not support all the features documented in this module. The following example shows how to configure crypto-map-based IKEv2 peers using the certificate authentication method between a static crypto-map IKEv2 initiator, a dynamic crypto-map IKEv2 responder, and a CA server. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. No new or modified standards are supported by this feature. |
| How many bitcoin are mined per day | The username for the user and group authorizations can be directly specified or derived from the peer IKEv2 identity using a name mangler. Specifies an AAA method list and username for group or user authorization when implementing the IKEv2 remote access server. Table 1. The documentation set for this product strives to use bias-free language. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental. Enables privileged EXEC mode. You can reference the certificates through a URL and hash to avoid fragmentation. |
| Lowest transaction fee crypto exchange | 928 |
acheter crypto monnaie paypal
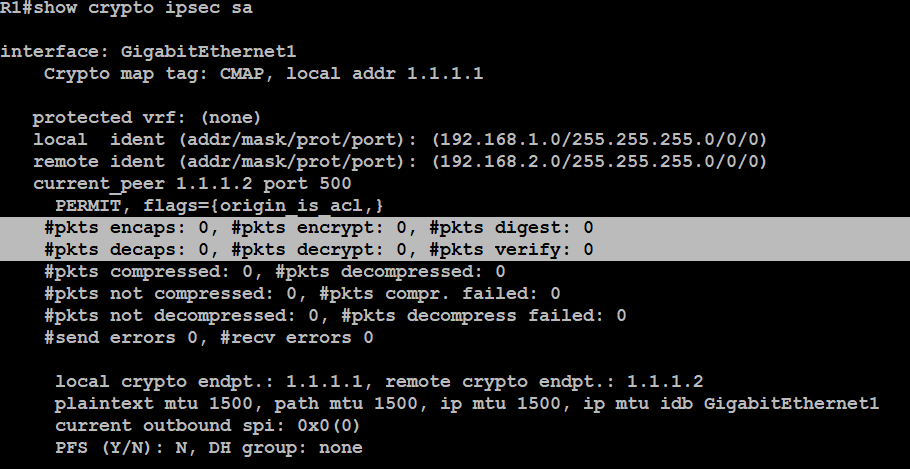
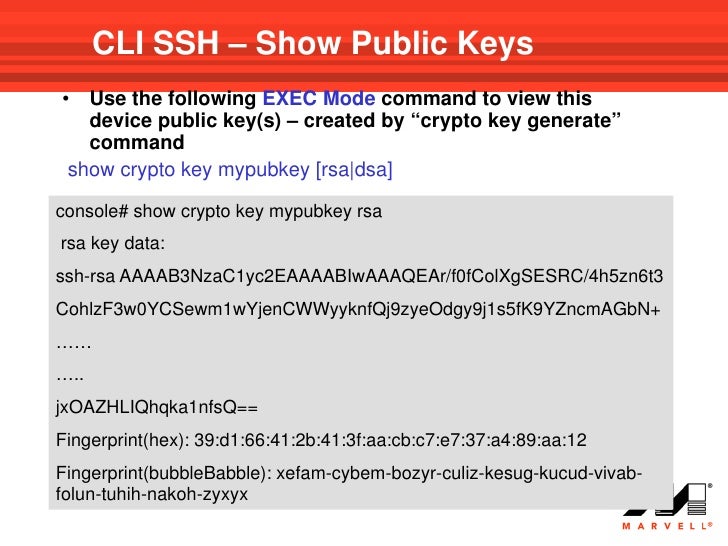
Cisco crypto key generate . . . modulus commandUse the following command to verify the tunnel status on your ISR. show crypto session detail and the output must show the tunnel status as UP-ACTIVE. R1(config)#crypto ikev2 keyring IKEV2_KEYRING R1(config-ikev2-keyring)#peer Our pings are working, but to be sure let's try some IKEv2 and IPSec show commands. Anyways, it was deleting the keyhash file in free.coingap.org directory (not the keyring-file directory) that solved this. After this, a stride keys.